The specified service namespace is invalid EventHub
When deploying an Event Hub using Azure Bicep, you may get the following error:
"code": "BadRequest", "message": "The specified service namespace is invalid. CorrelationId: 652cc73c-1fa7-450a-9788-b73ad6a818df"
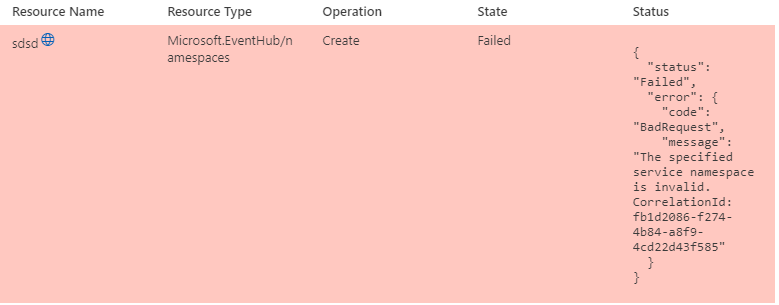
This could be caused by the name of your namespace needing to meet the naming requirements.