Implementing a Sandbox Environment in Microsoft Azure
When working with Microsoft Azure, you may want an environment for learning, whether for an individual or a team.
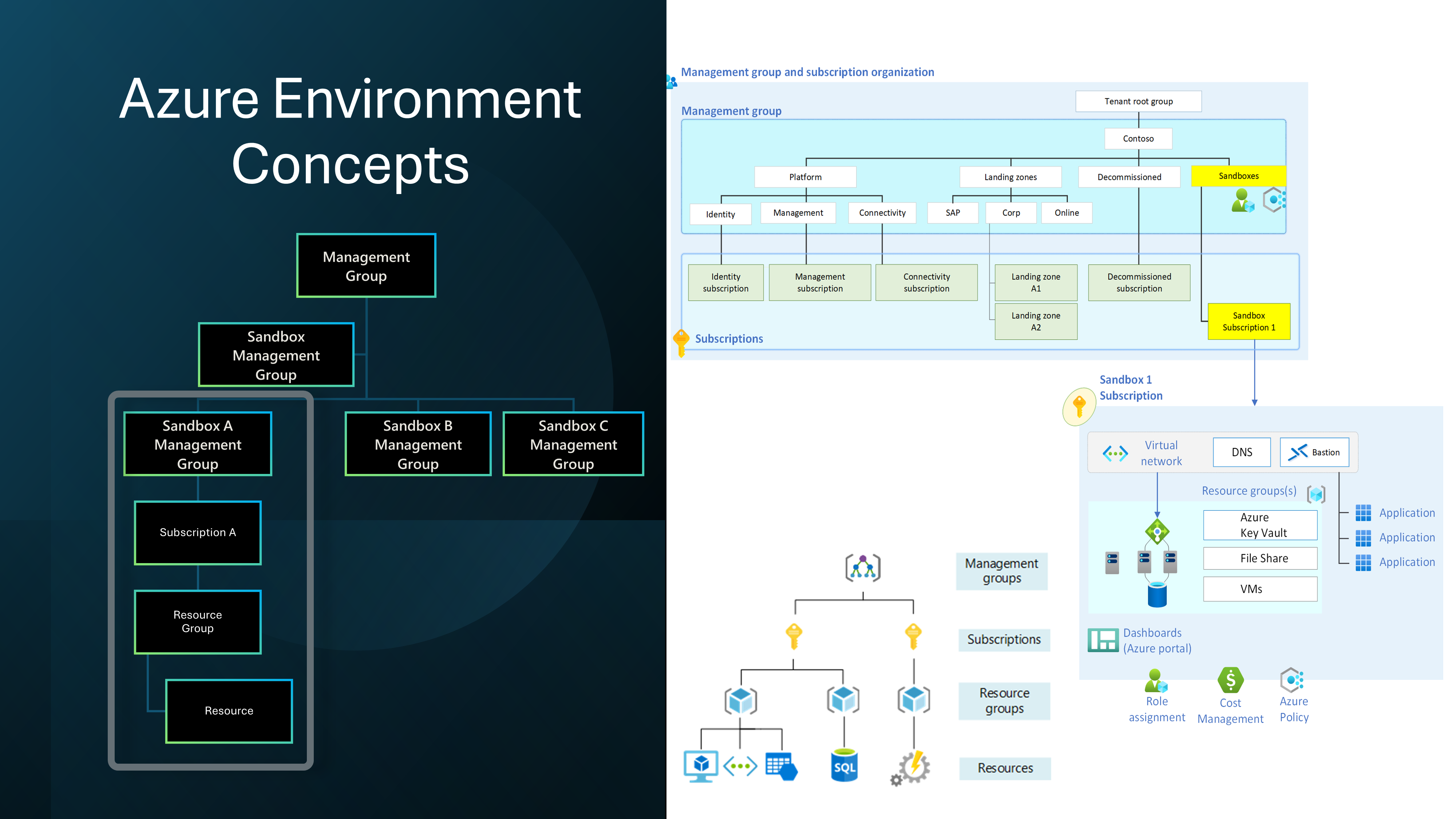
This article aims to highlight some reference implementation considerations for implementing a Sandbox environment within the Microsoft Azure platform.